Use facial, voice, or fingerprint recognition as a method of authentication for accessing systems, devices, or facilities. Confirm the identity of customers during transactions with zero effort but maximum precision, reducing the risk of identity theft and fraud, or get a more sophisticated system if your objective is a workers’ access system. Most suitable for online banking and phone-based customer service.

AI Security Solutions Development Services
What are AI Security Solutions and How Can They Help My Business?
Security solutions based on artificial intelligence are the systems that employ AI as the key technology and decision-making booster in their work. The main advantage of such systems is the application of an artificial intelligence algorithm that captures, learns, processes and employs information in different aspects of the security systems with mathematical precision.
Consequently, some de-facto benefits AI in network security offers are improved threat detection thanks to analytics and continuous monitoring, automated responses to certain types of security incidents, reducing false positives, and unloading your personnel working in security - either from a cost-saving or HR perspective.
AI Security Solutions Services We Provide
These days, artificial intelligence in security is yet to discover its full potential and complete list of ready-to-use solutions. Tap into what can be done now with Devox: let’s discover the exciting journey of AI in cybersecurity together.
-
Biometrics Recognition Software
-
Intrusion Detection Systems (IDS)
Creating systems that monitor network traffic and system activities for suspicious behavior, alerting administrators to potential security breaches. We are tailoring it to recognize a wide range of intrusion tactics and detect unusual patterns or behaviors, adapting to new threats through continuous learning.
-
Antivirus and Anti-Malware Software
Incorporating AI into the antivirus architecture to identify and block malware, including variants that haven’t been seen before, based on behavior and heuristic analysis: artificial intelligence identifies and neutralizes a wide array of malicious software, including viruses, worms, and ransomware.
-
Fraud Detection Systems
Developing systems that analyze transaction patterns and user behaviors to detect and prevent fraudulent activities in real-time. These systems are particularly useful in the financial sector, where they help in identifying unusual transactions that could indicate fraud.
-
SASE and Network Security Management
SASE frameworks often integrate AI to provide more dynamic and adaptive network access and security policies. AI algorithms help it manage and secure complex network infrastructures, identifying vulnerabilities, and automating responses to threats.
-
Security Information and Event Management (SIEM)
AI enhances SIEM solutions by improving their ability to analyze security logs and alerts, reducing response times, and minimizing false positives. Leverage AI potential to gather, analyze, and interpret vast amounts of data on emerging cyber threats from various sources.
Our AI Security Solutions Development Process
Benefits of Implementing AI Security Solutions
AI and machine learning in cyber security are perceived as game changers for a reason. Read how they will alleviate your protection and security experience to the better.
-
Immediate Threat Detection
Recognize patterns and anomalies that might indicate a security breach at once with the potential of cyber security in artificial intelligence. AI algorithms can analyze massive volumes of data at an exceptional speed, allowing for the early detection of potential threats and vulnerabilities and noticing threats traditional security methods wouldn’t.
-
Automated Incident Response
In the event of a cyberattack, every second counts: AI can automate responses to security incidents, significantly reducing response times. Rapid action can help contain and mitigate the impact of any attack, potentially saving your business from considerable losses and downtime.
-
24/7 Monitoring and Analysis
It’s hard to maintain with a human-only team if continuous monitoring is essential. Artificial intelligence in IT security provides around-the-clock surveillance of your network and digital assets. They continuously analyze data flows, user activities, and system behaviors to identify suspicious activities, ensuring constant vigilance against threats.
-
Adapt to Changing Security Requirements or Threat Landscapes
Strengthen your defenses proactively before an attack occurs. By leveraging machine learning and artificial intelligence in cyber security, your brand-new system will predict future threats and vulnerabilities based on historical data and emerging trends, easily scaling alongside your business and adapting to new types of cyber threats. They can be updated and trained with new data, serving as a flexible solution that evolves hand-in-hand with your business and the cybersecurity landscape.
-
Dealing with Sophisticated Cyber Attacks
Modern cyberattacks are becoming more sophisticated and harder to detect. AI, with its advanced algorithms, can evolve and learn to recognize new types of attacks, staying ahead of cybercriminals.
-
Reduce False Positives
AI can distinguish between genuine threats and benign anomalies more accurately than traditional systems. This precision reduces the number of false alarms, allowing your security team to focus on real issues.
-
Make it Easier for Your Staff
Overcome skill shortages the cybersecurity field often faces while simultaneously unloading your existing personnel. AI can handle routine tasks and analyses without adding complexity for end-users, allowing the existing security staff to focus on more complex and strategic activities while also benefiting from an enhanced user experience.
-
Better Regulatory Compliance
With AI's advanced monitoring and reporting capabilities, businesses can better adhere to regulatory requirements related to data protection and privacy. Identify and protect sensitive information, crucial for adhering to regulations like GDPR or HIPAA, and ensure swift action and documentation for regulatory audits with real-time alerts and detailed reporting.
Key Functionalities to Add to Your Custom AI Security Solutions System
Threat Detection and Analysis
AI systems are adept at identifying potential threats by analyzing vast data. They can detect anomalies, unusual patterns, or behaviors that might indicate a security breach, malware infection, or other types of cyberattacks.
Automated Incident Response
Upon detecting a threat, AI Security Systems can initiate automated responses. This could include isolating affected systems, blocking suspicious IP addresses, or deploying patches to vulnerabilities, thereby reducing the window of opportunity for attackers.
Behavioral Analytics
By using machine learning algorithms, AI systems can learn and understand normal network behavior. This understanding enables them to detect deviations that might signify a security incident, such as unauthorized access or data exfiltration attempts.
Predictive Capabilities
AI can use historical data and current trends to predict potential security incidents before they happen. This predictive analysis helps in proactively strengthening security measures.
Continuous Monitoring
AI systems offer round-the-clock monitoring of networks and systems, providing constant vigilance and immediate detection of any suspicious activities.
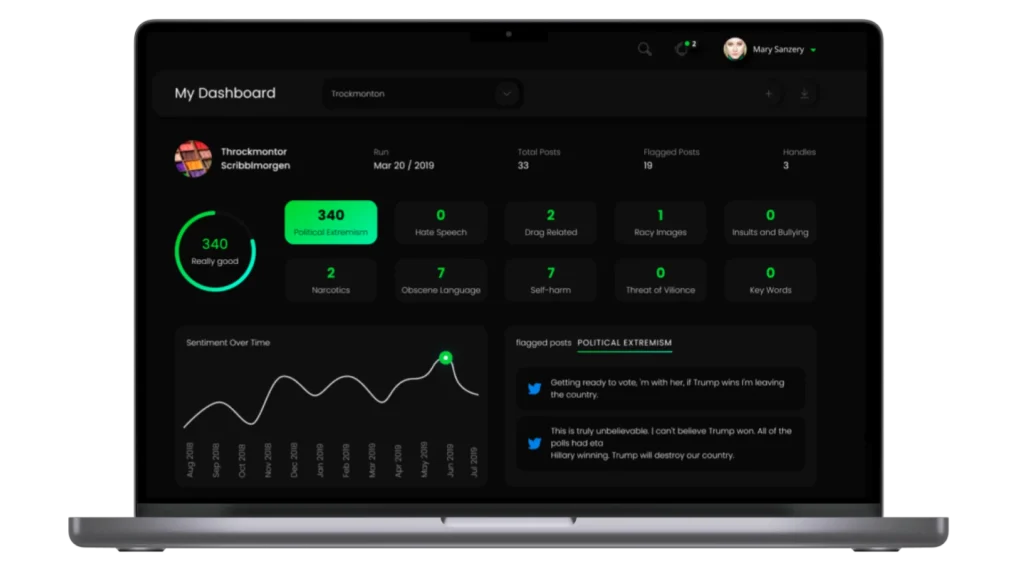
User and Entity Behavior Analytics (UEBA)
These systems can profile and monitor user behavior, identifying potentially risky actions that deviate from normal patterns, which might indicate compromised accounts or insider threats.
Data Protection
Implements advanced algorithms for ensuring the security and privacy of data, including encryption, access control, and data loss prevention techniques.

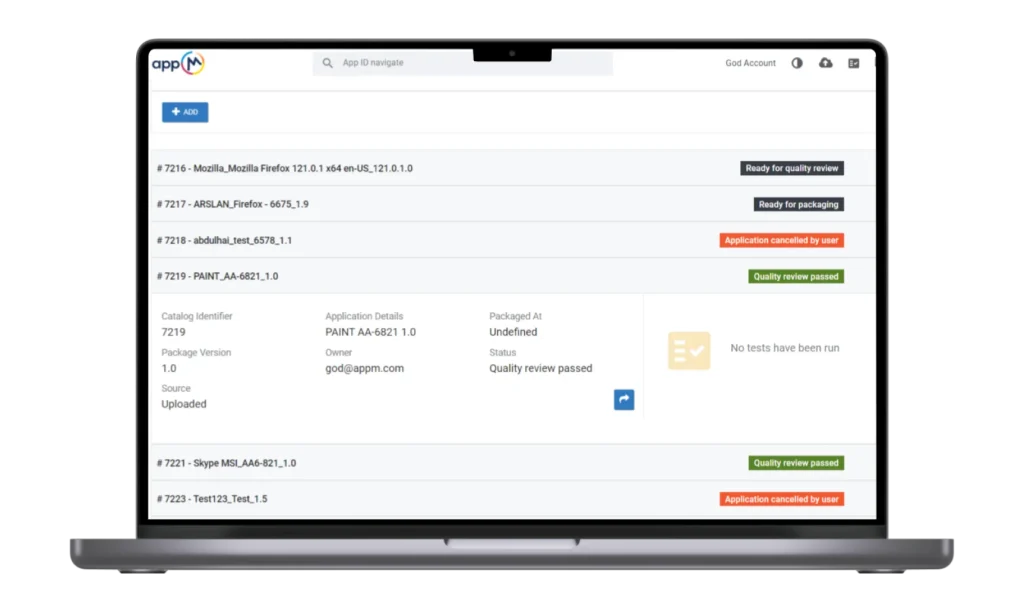
Juriba: Enterprise Digital Workplace Management Platform for Migration & Automation
An enterprise-grade automation platform that streamlines IT project workflows through smart dashboards.
Additional Info
- .NET 6
- MS SQL
- Redis
- Angular
- NgRx
- RxJS
- Kubernetes
- Elasticsearch
United Kingdom
Trusted by
Industry Contribution Awards & Certifications
Testimonials
FAQ
-
Will artificial intelligence or cyber security be more prolific in the future?
In the future, artificial intelligence AI in cyber security market is set to be highly prolific, but in interconnected ways. AI’s influence is expanding across various sectors, driving innovation and efficiency; meanwhile, the increasing digitalization of society makes cybersecurity more crucial than ever for protecting data and systems. The two fields are interdependent: artificial intelligence enhances cybersecurity efforts through advanced threat detection and response, while robust cybersecurity is vital for safeguarding AI systems.
As technology advances, both AI and cybersecurity will face new challenges and opportunities, indicating significant growth and evolution in both areas. The future landscape will likely see these fields not as separate entities, but as complementary forces shaping the digital world.
-
How does artificial intelligence work in cyber security?
Artificial intelligence in cyber security projects works by utilizing advanced algorithms and machine learning techniques to enhance threat detection, response, and prevention. AI systems analyze vast amounts of data from network traffic, user behavior, and other sources to identify patterns and anomalies that indicate potential threats, such as malware or unauthorized access. These systems learn over time, improving their accuracy in detecting new and sophisticated cyber threats.
Artificial intelligence also automates responses to identified threats, reducing response times and mitigating potential damage. Additionally, AI assists in predictive analysis, foreseeing potential vulnerabilities before they are exploited. This makes cybersecurity more proactive, efficient, and adaptive to evolving cyber threats.
-
How does artificial intelligence help us in cyber security?
Artificial Intelligence aids cybersecurity by providing advanced threat detection, enhancing response times, and reducing human error. AI algorithms can process vast amounts of data quickly, identifying potential threats like malware or unusual network patterns that might elude traditional methods. Machine learning enables these systems to learn from previous incidents, improving their ability to detect new and evolving cyber threats.
AI also automates responses to security breaches, allowing for immediate action to mitigate damage. Additionally, its predictive capabilities help forecast future vulnerabilities, enabling proactive defense measures. This integration of AI in cybersecurity results in more robust and adaptive protection against a wide range of digital threats.
-
How do AI Security Solutions ensure compliance with data protection regulations?
Our AI Security Solutions are designed with a compliance-first approach. They include features like automated data audits, real-time compliance monitoring, and advanced data encryption to ensure adherence to regulations like GDPR, HIPAA, and CCPA. For instance, our solutions automatically flag and report any unauthorized access to sensitive data, helping businesses maintain high standards of data privacy and regulatory compliance.
-
Can AI Security Solutions be integrated with existing security systems?
Yes, our AI Security Solutions are designed for seamless integration with existing security infrastructures. We ensure compatibility with a wide range of legacy systems and security software, enhancing their capabilities with AI-driven analytics and threat detection. For example, our solutions can integrate with existing SIEM systems to provide more advanced anomaly detection and predictive threat analysis.
-
What advancements in AI Security Solutions can we expect in the near future?
The role of artificial intelligence in cyber security is expected to grow with time. Future development will more likely include greater predictive capabilities using deep learning, enhanced automated response systems, and more sophisticated behavioral analytics for insider threat detection. Advancements in quantum computing are also anticipated to revolutionize encryption methods, making AI-driven security systems even more robust against emerging cyber threats.
-
How does the implementation of AI Security Solutions impact the overall cybersecurity workload?
The application of artificial intelligence in security significantly reduces the cybersecurity workload by automating routine tasks such as traffic analysis, log monitoring, and incident response. For example, our AI systems can autonomously manage thousands of security events per second, freeing up your cybersecurity team to focus on more strategic tasks and reducing the need for large-scale manual interventions.
Want to Achieve Your Goals? Book Your Call Now!
We Fix, Transform, and Skyrocket Your Software.
Tell us where your system needs help — we’ll show you how to move forward with clarity and speed. From architecture to launch — we’re your engineering partner.
Book your free consultation. We’ll help you move faster, and smarter.
Let's Discuss Your Project!
Share the details of your project – like scope or business challenges. Our team will carefully study them and then we’ll figure out the next move together.
Thank You for Contacting Us!
We appreciate you reaching out. Your message has been received, and a member of our team will get back to you within 24 hours.
In the meantime, feel free to follow our social.
Thank You for Subscribing!
Welcome to the Devox Software community! We're excited to have you on board. You'll now receive the latest industry insights, company news, and exclusive updates straight to your inbox.